Tag: Cyber Security
-
Law Firm and Corporate Cybersecruity Presentation – UMB
By Joseph Raczynski Recorded at the University of Maryland, Baltimore during the “Cybersecruity and You” morning session. Discussed is the current landscape of cybersecurity at law firms and corporations, the primary issues these organizations are finding and general awareness of what is happening.
-

LegalSEC: Email Security is Priority One for Law Firms
By Joseph Raczynski BALTIMORE, Md. — “Three strikes and you are out of the firm.” This is the mantra of one law firm when dealing with employees who click on spear-phishing emails, according to Mounil Patel, Strategic Technology Consultant at Mimecast, an email and cloud security firm. Patel’s comments came at the recent gathering of…
-
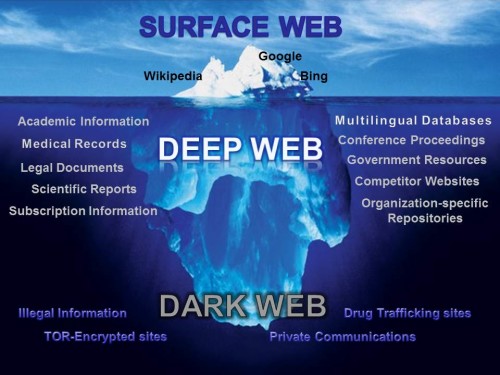
LegalSEC: Shedding Light on the Dark Net
By Joseph Raczynski The importance of law firms understanding the dark web Your very sensitive private client data could be available for all to see on the Internet right now. Technically this data would be on the Dark Net or Dark Web. It is the portion of the World Wide Web that is hidden or…
-
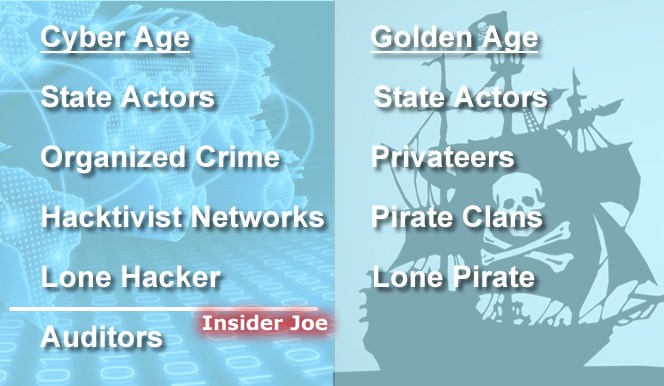
LegalSEC: Cybersecurity, Rooted in 500 Years of History
By Joseph Raczynski Learning from colonial piracy about the war on cybersecurity “It is a small world. It’s a fragile world. No one is safe until everyone is safe.” These are the cautionary words of Rod Beckstrom of The Rod Beckstrom Group, the keynote speaker at the cybersecurity LegalSEC Summit last week in Baltimore. With…
-

State of the Cloud at Law Firms: The Interstitial Phase of Law Firm Cloud Philosophy
By Joseph Raczynski The word “Cloud” can be a divisive word at law firms. Recently uttering the term during technology meetings with East Coast-based law firms with between 50 and 3,000 attorneys elicited starkly differing responses based on firm size and practice dominance. Most of the midsized firms with whom I have met over the…
-

-

The Paralegal’s Role in the New World of Cybersecurity
Published: The Legal Intelligencer Written: Victor Panieczko Contributor: Joseph Raczynski Cyberattacks have affected virtually every industry. These include, but are not limited to, health care, education, finance, energy, retail, hospitality and government. Most of us have seen or heard about the security breaches of Home Depot Inc., eBay Inc., Target Corp., Sony Pictures Entertainment, JPMorgan…
-

Security Breaches Trending Ever Higher at Law Firms: Cybersecurity and the Actual Threats Firm See Today
By Joseph Raczynski Security is the number one anxiety for law firm management. After visiting with numerous law firms spanning the East coast over the past month, the anecdotal evidence is rich. These independent accounts from large- and medium-sized law firms alike reaffirm the data presented in the recently released American Bar Association’s 2015 Legal…
-

The Anatomy of Successful Cyber Attacks
By Joseph Raczynski Preparation for cyberattacks on your network requires a fundamental understanding of the complete picture of who has launched the assault. Steve Surdu of Surdu Consulting, LLP gave the keynote address at ILTA LegalSEC Summit 2015 in Baltimore, MD describing “The Anatomy of Successful Cyber Attacks.” Steve outlined four attacker or threat profile group…
-

The World of Advanced Endpoint Security
By Joseph Raczynski Surprisingly the vendors in cybersecurity differ on their approaches to protecting your law firm. At the ILTA LegalSEC Summit 2015 in Baltimore, MD they had a panel discussion on how each vendor tackles the ever bounding threats. For background when this post refers to endpoint security I am describing securing the user at…
-

From Russia (and Asia) with Love: Cyber Warfare and the growth of State-Sponsored Hacking
By Joseph Raczynski The 5th Annual Law Firm CFO/CIO/COO Forum The scope of the threats to law firm data is global. In this panel discussion at the Data Privacy, Security & the Globalized Law Firm CFO/CIO/COO Forum, a country by country breakdown of dangers were discussed while the audience absorbed the magnitude of the panels…
-
What the Hack is going on lately?
By Joseph Raczynski The concussion from the bombardment of computer code is silent, though the havoc wreaked is deafening. Cyber-attacks have escalated in scope and frequency in the last five months affecting finance, creditability, and confidence in the private and public sector. What is going on and why? There are several fronts in this battle. …

