Category: Security
-

Anthropic’s Jack Clark, on The Architecture of Intelligence – When Models Break the Sandbox
At the recent Semafor World Economy summit, held against the backdrop of the World Bank and IMF Spring Meetings, the air was thick with a new kind of systemic risk. This wasn’t about subprime mortgages or sovereign debt; it was about Agentic AI, models that don’t just answer questions, but act on the world. Jack…
-

Securing DeFi: The Immunefi Behind the Code with Mitchell Amador
TOKEN2049, Singapore: Recently I sat down with Mitchell Amador, the visionary CEO and cofounder of Immunefi, who continues to shape the future of blockchain security through his unwavering drive to make the Web3 ecosystem more resilient and transparent. Under his leadership, Immunefi has become the gold standard for smart contract protection, transforming how protocols defend themselves…
-
Tech Snippets Today – Perry Carpenter – Chief Human Risk Management Strategist – KnowBe4
Today, any image, video, or audio can be fabricated to extent that it is nearly, or almost impossible to tell. This show focuses on how we can combat AI deepfakes, deception and disinformation. My guest Perry Carpenter – Chief Human Risk Management Strategist at KnowBe4 has written a book, “FAIK: A Practical Guide to Living…
-
Tech Snippets Today – Asher Lohman – VP of Data & Analytics at Trace3 with Joseph Raczynski
Today, we uncover how AI is reshaping the fight against fraud! With Asher Lohman, VP of Data Analytics at Trace3 we’ll crack open the magic of machine learning—spotting sneaky behavior, detecting anomalies, and sending real-time alerts faster than ever. Can AI outsmart fraudsters while keeping pace with their tricks? You’re about to find out—let’s dive…
-

Tech Snippets Today at NEARCON – Immunefi – Mitchell Amador, CEO with Joseph Raczynski
One of the most important areas in the blockchain space is around testing smart contracts. Since everything is reliant on code, the key is to identify potential holes in contracts, which could lead to massive breaches or losses of money. Immunefi is a place where hackers and companies meet to help find bugs in code…
-

Cybersecurity at the centre – competing globally with different rules
Originally published on Legal Insights Europe. By Joseph Raczynski The topic of global cybersecurity will challenge each one of us. It is an unstable concoction of cultural norms and legal property rights patiently awaiting attention before it bursts. The overarching question is ‘how can legal organizations and overall society manage rising threats to the integrity of…
-

Leveraging blockchain to decrease data breaches, increase security
Originally published in Thomson Reuters By Joseph Raczynski In the not-too-distant future, blockchain will get personal – very personal. That’s a good thing when it comes to integrity of your digital identity. The Internet is a complex space for identity management. Every site has a login and password, and those sites which have federated their…
-

ILTACON 2016 SESSION: NEW INTERNATIONAL STANDARD FOR CLOUD DUE DILIGENCE
The cloud is becoming increasingly ubiquitous at law firms. In fact, a recent ABA Technology Survey stated that 46 percent of cloudless firms will be transitioning in the next 6-12 months. In the session on the “New International Standard for Cloud Due Diligence,” Gregg Brown, senior director Technical Strategy, Computer Standards at Microsoft, and Patrick…
-
Law Firm and Corporate Cybersecruity Presentation – UMB
By Joseph Raczynski Recorded at the University of Maryland, Baltimore during the “Cybersecruity and You” morning session. Discussed is the current landscape of cybersecurity at law firms and corporations, the primary issues these organizations are finding and general awareness of what is happening.
-

LegalSEC: Email Security is Priority One for Law Firms
By Joseph Raczynski BALTIMORE, Md. — “Three strikes and you are out of the firm.” This is the mantra of one law firm when dealing with employees who click on spear-phishing emails, according to Mounil Patel, Strategic Technology Consultant at Mimecast, an email and cloud security firm. Patel’s comments came at the recent gathering of…
-
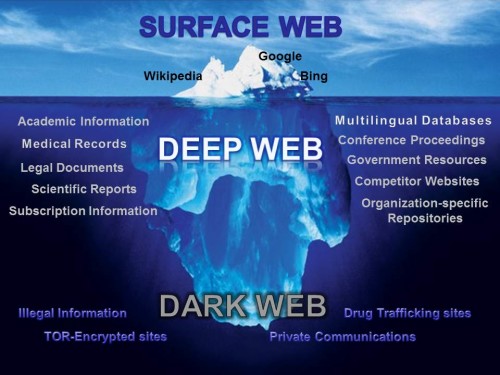
LegalSEC: Shedding Light on the Dark Net
By Joseph Raczynski The importance of law firms understanding the dark web Your very sensitive private client data could be available for all to see on the Internet right now. Technically this data would be on the Dark Net or Dark Web. It is the portion of the World Wide Web that is hidden or…
-
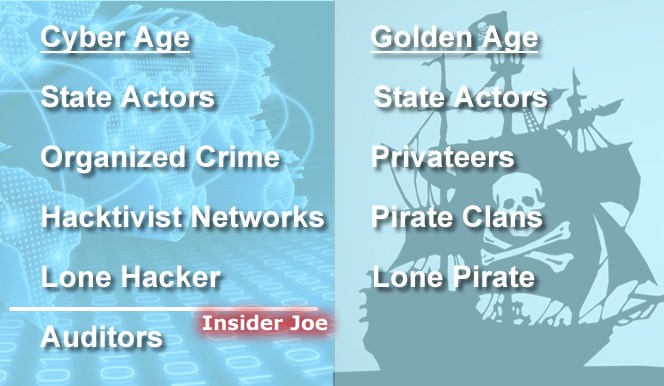
LegalSEC: Cybersecurity, Rooted in 500 Years of History
By Joseph Raczynski Learning from colonial piracy about the war on cybersecurity “It is a small world. It’s a fragile world. No one is safe until everyone is safe.” These are the cautionary words of Rod Beckstrom of The Rod Beckstrom Group, the keynote speaker at the cybersecurity LegalSEC Summit last week in Baltimore. With…
-

-

The Paralegal’s Role in the New World of Cybersecurity
Published: The Legal Intelligencer Written: Victor Panieczko Contributor: Joseph Raczynski Cyberattacks have affected virtually every industry. These include, but are not limited to, health care, education, finance, energy, retail, hospitality and government. Most of us have seen or heard about the security breaches of Home Depot Inc., eBay Inc., Target Corp., Sony Pictures Entertainment, JPMorgan…
-

ILTA’s 2015 Annual Technology Survey Security Highlights
By Joseph Raczynski Security weighs heavily on this year’s survey It’s out! The 2015 International Legal Technology Associations Annual Survey is stocked with insightful legal technology industry knowledge. This is always an exciting time of the year for me as I get to compare and contrast the stories I heard during the year from law…
-

Security Breaches Trending Ever Higher at Law Firms: Cybersecurity and the Actual Threats Firm See Today
By Joseph Raczynski Security is the number one anxiety for law firm management. After visiting with numerous law firms spanning the East coast over the past month, the anecdotal evidence is rich. These independent accounts from large- and medium-sized law firms alike reaffirm the data presented in the recently released American Bar Association’s 2015 Legal…
-

The Anatomy of Successful Cyber Attacks
By Joseph Raczynski Preparation for cyberattacks on your network requires a fundamental understanding of the complete picture of who has launched the assault. Steve Surdu of Surdu Consulting, LLP gave the keynote address at ILTA LegalSEC Summit 2015 in Baltimore, MD describing “The Anatomy of Successful Cyber Attacks.” Steve outlined four attacker or threat profile group…
-

Law Firm Security Architecture 101
By Joseph Raczynski In a granular overview of the appropriate security procedures a law firm should have in place, Douglas Brush, Director ISG, Kraft Kennedy; Brad Bragg, CIO Womble Carlyle; Scott Rolf, CIO, Tucker Ellis, LLP; and Tim Golden, Manager, Enterprise Architecture & IT Governance, McGuireWoods; discussed “Security Architecture 101” at the ILTA LegalSEC Summit 2015 in Baltimore, MD.…
-

Keeping It Secure – Internet in a Bubble
By Joseph Raczynski Absolutely! Feel free to use YouTube, Twitter, Facebook and Gmail for business purposes at Kelley Drye. As many firms struggle with internal access to these services for their employees, Kelley Drye has figured out how to satisfy employees and firm management by establishing a secure secondary path to the Internet in a…
-

The World of Advanced Endpoint Security
By Joseph Raczynski Surprisingly the vendors in cybersecurity differ on their approaches to protecting your law firm. At the ILTA LegalSEC Summit 2015 in Baltimore, MD they had a panel discussion on how each vendor tackles the ever bounding threats. For background when this post refers to endpoint security I am describing securing the user at…
-

From Russia (and Asia) with Love: Cyber Warfare and the growth of State-Sponsored Hacking
By Joseph Raczynski The 5th Annual Law Firm CFO/CIO/COO Forum The scope of the threats to law firm data is global. In this panel discussion at the Data Privacy, Security & the Globalized Law Firm CFO/CIO/COO Forum, a country by country breakdown of dangers were discussed while the audience absorbed the magnitude of the panels…
-

Enemies at the Gate: Responses to Data Security Threats at Law Firms
By Joseph Raczynski The 5th Annual Law Firm CFO/CIO/COO Forum In eerie silence, law firms could be easily breached like JPMorgan Chase, Home Depot and Sony by cyber criminals. The difference with law firms, few would know the sensitive data was absconded. While law firms do not have to report such penetrations we learned at…
-

eDiscovery: Backup and Cloud Safeguards
By Joseph Raczynski “Not preparing for eDiscovery will cause your company to spend millions meeting an eDiscovery request via a lawsuit or investigation or worse losing a multi-million or multi-billion dollar law suit because you cannot retrieve data in time to satisfy a judge.” These were the ominous words from Curtis Preston, CEO, of Truth…
-

Law Departments and Cyber Security: Addressing the Scary Stuff
By Joseph Raczynski Law firm security bears one of the softest underbellies within the world of professional services. This alarm was sounded during an ILTA panel discussion surrounding security with Michael Russell of Liberty Mutual, Brian Donato of Vorys Sater, and Natalie Fedyuk of KPMG. The consensus from the group was that law firms have…
-

Missing Insurance Payments?
By Joseph Raczynski What if your life insurance company looked to find ways to discontinue payments, but not to locate beneficiaries who were missing payments owed to them? Well it happened and one major life insurance company has recently settled a law suit where they must pay nearly $500 million to people across the United…
-

New Phishing Scams Can Hook Ya!
By Joseph Raczynski Many moons ago when phishing scams were first cast they were easy to detect. The bait was rank with punctuation and spelling errors and the emails were typically all text. You viewed the email from Bank of X, cocked your head to the side and then easily dismissed it as chum. Surprisingly…
-

Potential Fraud: Who’s Web Watching You? Answers you can finally see!
By Joseph Raczynski Who really knows you? Is it your friends, the government, or could it be the companies on the web that have the best sights? Well, do not be astonished if it is the latter. Online companies may be better acquainted with you than your family. Fortunately, you can actively in an intuitive…
-
What the Hack is going on lately?
By Joseph Raczynski The concussion from the bombardment of computer code is silent, though the havoc wreaked is deafening. Cyber-attacks have escalated in scope and frequency in the last five months affecting finance, creditability, and confidence in the private and public sector. What is going on and why? There are several fronts in this battle. …
-

Eyes, Now Telling More Secrets
By Joseph Raczynski -Iris scan identity verification now being dispatched Ethan Hunt clad in black slips through the skylight’s slight gap and drops forty feet down on a line in the shadow of night. Pouncing upon his suspect as he sleeps, Hunt pulls out the iris scanner and captures the eye image of the criminal…

