Category: Dark Web
-

Top 10 err.. 16 LegalTech Talks of 2021! Now available!
The list is out! Last year was an amazing one for LegalTech talks and thought leadership. I presented over 70 times on Blockchain, Cryptocurrency, AI, Workflow, and the Legal Platform. It was also a fascinating year where edgy concepts entered the LegalTech space, including the Metaverse and NFTs. In all likelihood, these will continue to…
-
Video: Generate 2018 – Darkside of the Web
Have you wondered what is going on these days on the Web with cybersecurity for Law Firms? This is a deep dive and more information on how a hacker goes after IoT devices from the Generate Conference in London.
-

The vice grip of cybersecurity concerns on law firms
Originally published on Legal Insights UK & Ireland By Joseph Raczynski Law firms stand in a very precarious position in the cybersecurity world. Next to financial institutions, private legal institutions are a virtual honey pot for cybercriminals. Any breach, no matter the size, impacts the client, and certainly could destroy a firm’s reputation. Four years ago,…
-

Cybersecurity Trends and The Dark Web in Legal (VBlog)
By Joseph Raczynski The latest video on Cybersecurity as it relates to the Legal industry. This was recorded for Thomson Reuters across all business units.
-

How prepared are law firms to face cyber security threats?
By Joseph Raczynski The hacking of Panamanian law firm Mossack Fonseca last April resulted in 11.5 million leaked attorney-client privileged documents, exposing the widespread use of off-shore businesses by wealthy individuals and corporations around the world and highlighting the imperative need for proactive measures against corruption and other illicit financial activity. But what it also…
-
Law Firm and Corporate Cybersecruity Presentation – UMB
By Joseph Raczynski Recorded at the University of Maryland, Baltimore during the “Cybersecruity and You” morning session. Discussed is the current landscape of cybersecurity at law firms and corporations, the primary issues these organizations are finding and general awareness of what is happening.
-
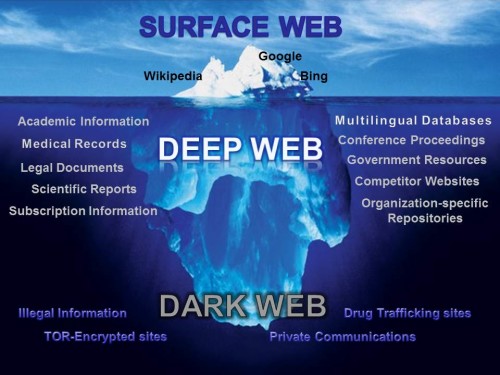
LegalSEC: Shedding Light on the Dark Net
By Joseph Raczynski The importance of law firms understanding the dark web Your very sensitive private client data could be available for all to see on the Internet right now. Technically this data would be on the Dark Net or Dark Web. It is the portion of the World Wide Web that is hidden or…
