Tag: Joseph Raczynski
-
x402
For nearly three decades, a ghost has haunted the infrastructure of the World Wide Web. Buried deep within the hyper-text transfer protocol, the very language browsers and servers use to speak to one another, sat a reserved, unused status code. You know 200 (OK). You definitely know 404 (Not Found) and probably 500 (Internal Server…
-

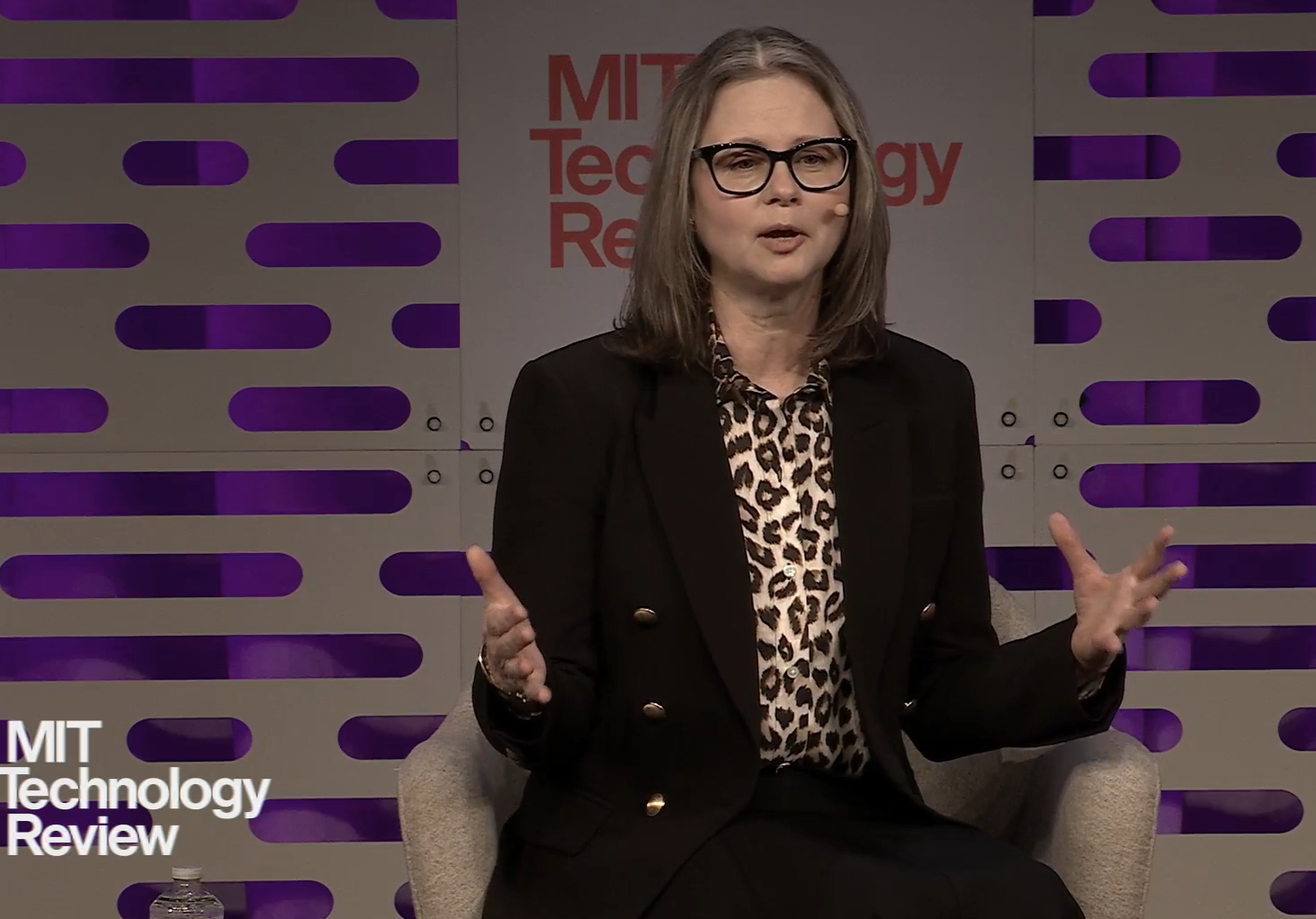
AI at the Speed of Enterprise R&D: Isomorphic Labs and the Future of Drug Discovery
EmTechMIT, Cambridge, MA: In recent years, enterprise R&D in biotechnology has been fundamentally reshaped by the rise of artificial intelligence. At EmTechMIT, Chief Business & Legal Officer Sarah Korman of Isomorphic Labs (ISO), the Alphabet-backed spinout from Google’s DeepMind, offered a behind-the-scenes look at how AI is accelerating the design and development of novel medicines,…
-

Digital Gold Rush: Tokenizing the Oldest Asset on Earth with Curt Hopkins
Recently, gold hit multiple all-time highs in its valuation. Gold prices have risen recently due to a combination of factors, including geopolitical tensions, economic uncertainty, and strong demand from central banks and individual investors. But now…Gold has a new vehicle for people onboard it into their portfolios, Blockchain. Today I am very curious to hear…
-

The Power of Choice: Rethinking Agency in the Age of AI
EmTechMIT, Cambridge, MA: At the MIT Media Lab, few voices blend data science, social theory, and design for human agency as fluently as Professor Alex “Sandy” Pentland. His talk at EmTechMIT, titled “The Power of Choice,” was not about the power of technology itself, but about how to realign it around the individual. Pentland offered…
-

Inside Tezos: The Mathematician Rewriting Blockchain’s Rules with Arthur Breitman
If you’ve ever wondered what happens when a mathematician, robo-engineer, and blockchain pioneer walk into a room, today’s guest is the punchline. Arthur Breitman, co-founder of Tezos, brings a background spanning competitive coding, Wall Street, and even self-driving cars to the world of blockchain innovation. We’ll dig into how Arthur’s science chops helped architect Tezos, a…
-

The Changing Face of Friendship – The Race to AI Intimacy
EmTechMIT, Cambridge, MA: Camille Carlton began with a chilling observation: “Many people find it easy and some satisfying to engage in ongoing relationships with AI. This development has ramifications for our psychological and social health that we’re just beginning to unravel.” Carlton, a policy advocate at the Center for Humane Technology, addressed not only the…
-

Building Customer Trust through AI
EmTechMIT, Cambridge, MA: Brian O’Kelley, a pivotal figure in digital advertising since the early 2000s, opened his talk by observing that the very fabric of internet advertising is undergoing a seismic transformation as AI accelerates the death of traditional web channels. “Advertising is not going away anytime soon but the Web is already on its…
-

From AI Assistants to Associates
EmTechMIT, Cambridge, MA: Sudheesh Nair, Cofounder & CEO of TinyFish, opened his talk with a bold premise: AI agents are approaching a pivotal transformation, ready to change the very shape of the Internet by evolving from simple assistants to fully capable “associates”, collaborators and actors that handle real-world tasks across domains like hospitality, commerce, and…
-

Cardano and the Evolution of Trust in Web3 Finance with Frederik Gregaard
Cardano is the 10th largest cryptocurrency by market cap, sitting around 22.5 Billion dollars. That’s quite a number given its ICO raised approximately $62 million from 2015-2017 at a price of $0.0024. Cardano is part of what I call the old guard of cryptocurrencies launched after Ethereum, by Charles Hoskinson, which launched the era of…
-
The Agentic Workday: Redefining Work with AI Agents
EmTechMIT, Cambridge, MA: AI is not just an accessory, it is becoming the beating heart of how work happens in the most forward-looking organizations. In “The Agentic Workday,” Colette Stallbaumer, GM of Microsoft Copilot and co-founder of Microsoft’s WorkLab, unpacked how the rise of AI agents is reshaping workflows, expectations, and the very nature of…
-
The ABC’s of AI: Algorithms, Borders, Controls
EmTechMIT, Cambridge, MA: The rapidly evolving landscape of artificial intelligence, the algorithms that define it, the national borders that increasingly limit it, and the controls industries and governments seek to assert, stood front and center during this session. “The ABC’s of AI: Algorithms, Borders, Controls,” led by R. David Edelman of MIT and Fiona Murray…
-
The Speed of Trust: Jeff Feng and the Rise of Sei Labs
TOKEN2049, Singapore: It was fascinating to catch-up with Jeff Feng is the cofounder of Sei Labs. He is one of the most ambitious forces redefining the future of blockchain infrastructure. Before venturing into Web3, Feng built his career in high finance, first as an investment banker at Goldman Sachs and later as a venture investor at…
-

Protecting the Open Web Economy
EmTechMIT, Cambridge, MA: When Matthew Prince, Co-Founder and CEO of Cloudflare, took the EmTechMIT stage in Cambridge, he delivered what felt less like a keynote and more like a wake-up call for the digital economy. His talk, titled Protecting the Open Web Economy, was a sharp analysis of how artificial intelligence is quietly rewriting the…
-

Seamless Crypto in Your Chat: Wallet in Telegram with Irina Chuchkina
TOKEN2049 – Singapore: I had a very interesting conversation with Irina Chuchkina, Chief Growth Officer of Wallet in Telegram, who leads one of the most innovative projects in crypto integration within mainstream apps today. Wallet in Telegram is a built-in cryptocurrency wallet seamlessly embedded into the Telegram messaging app, empowering users to send, receive, and manage…
-

What’s the Buzz at TOKEN2049 Singapore – Thoughts from Joseph Raczynski
Here is my take having participated and witnessed all that was Token2049 Singapore 2025. My take, it’s a vivid confirmation that crypto is no longer a frontier of speculation but a foundational pillar of the next decade’s financial infrastructure, known as DeFi. The spotlight on Real World Assets (RWAs) tokenization highlighted how traditional assets are…
-
Harvard Business Review Article – AI Will Downsize Your Workforce. Upgrade Your Hiring Strategy Now
I had the distinct privilege to collaborate on an article for HBR (original article here: Harvard Business Review) with author Atta Tarki about the future of hiring and what you can do now. Professional services firms such as blue-chip law firms and management consultancies have long relied on a simple talent strategy: hire large amounts…
-

Crypto at Checkout – Living on Crypto – Real World Payments with April Pollock
Today we’re diving into one of the most practical use cases for crypto, actually spending it. For years people have joked, “Sure, you can buy Bitcoin, but can you buy a coffee with it?” Well, Bitrefill has been answering that question with a resounding yes since 2014. Operating in over 180 countries and partnering with countless major…
-

HR 4.0: Where Humans Meet AI with Oksana Day
If you’ve ever wondered how technology is reshaping the world of Human Resources, beyond outdated forms and awkward onboarding videos, we’re here to help. I’m thrilled to be joined by Oksana, a leading voice from Flex HR, an organization at the forefront of modern workforce transformation. We’ll start by exploring how digital tools and AI…
-

Beyond Cash: Stablecoins and the Future of Finance
With the GENIUS Act now passed into law, and everyone from Deutsche Bank, Apple, and Airbnb already paying attention, it’s clear that stablecoins are fast becoming core infrastructure for next-gen financial markets. We will get into why stablecoins matter and what it may mean for banks, companies and you. Will Beeson, former head of tokenized asset infrastructure at Standard…
-

The Dark Dawn: How Agentic AI Will Unleash an Unprecedented Cyber Criminal Renaissance
In the coming years, we will witness the emergence of cyber criminals armed with autonomous AI agents capable of conducting sophisticated, scalable attacks that will fundamentally overwhelm our current defensive capabilities, transforming isolated hackers into coordinated digital armies operating at machine speed. I have been tracking cybersecurity trends as a white hat hacker for the…
-
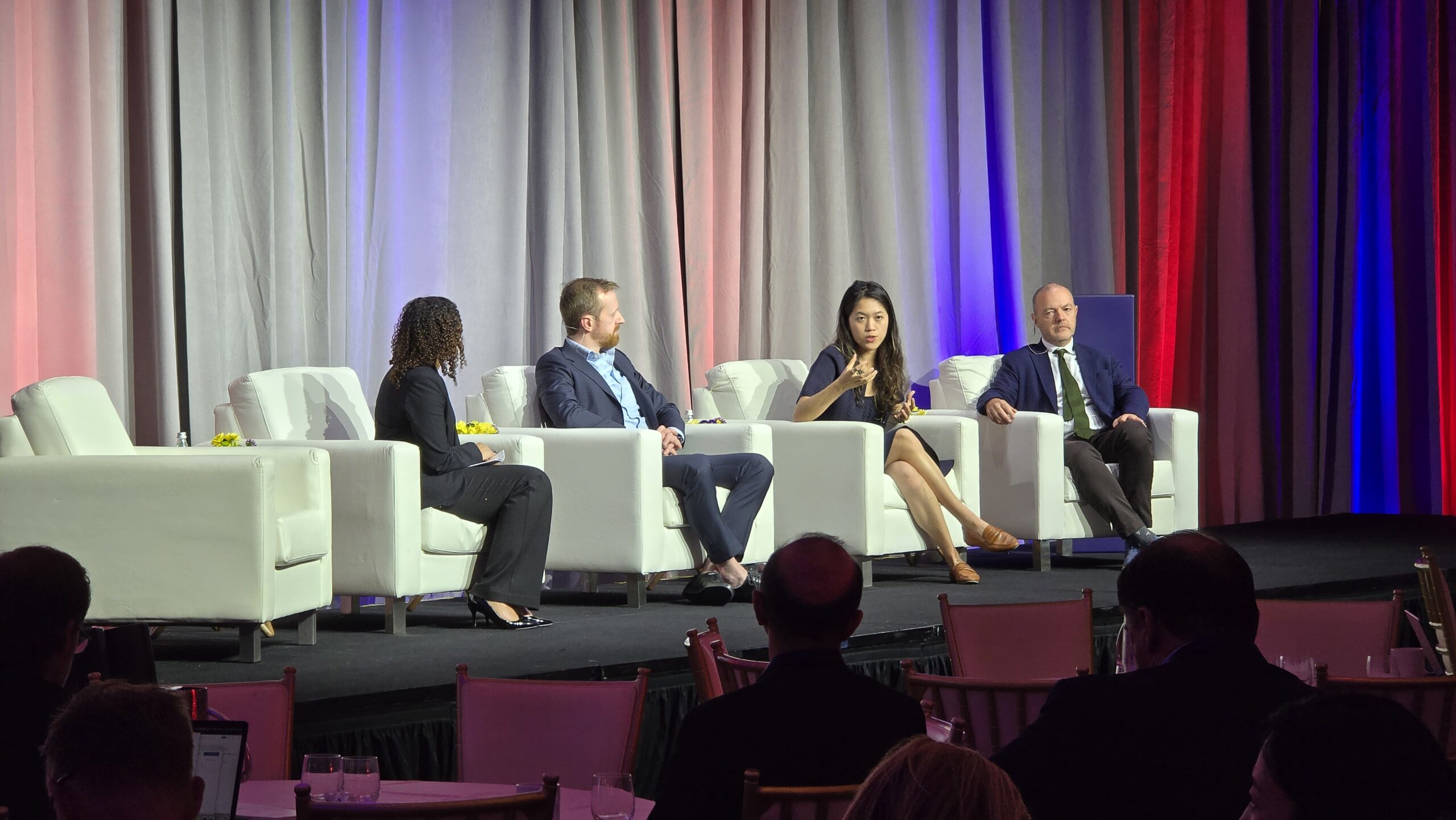
Bridging the Gap from Lab to Market: Insights from the AI+ Science Summit
At the AI+ Science Summit held at the Waldorf Astoria in Washington, D.C., a dynamic session entitled “Bridging the Gap from Lab to Market” convened leading voices from philanthropy, venture capital, and strategic science funding. Moderated by Nyah Stewart of SCSP, the panel, Vinny Beranek of Engine Ventures, Michelle Fang of Lux Capital, and Walter…
-

Science is National Security: Lessons from the AI+ Science Summit
At the AI+ Science Summit in Washington, D.C., the panel “Science is National Security” brought together thought leaders from government, industry, and the innovation economy to address a quietly radical thesis: scientific leadership has become the essential pillar of twenty first century power, as crucial to a nation’s security as the traditional tools of statecraft.…
-

Powering Innovation at the Intersection of AI & Science Highlights from the AI+ Science Summit
A Bold National Investment in AI and Science David McDonald framed the conversation by highlighting the scale and ambition of the NSF’s AI Institutes program over 500 million dollars invested in 40 plus centers nationwide, designed to accelerate scientific discovery through AI. These institutes span disciplines and blend academic, government, and industry partnerships to create…
-

Fireside Chat: Frontiers & Foundations – A Conversation with Jack Clark, Co-founder of Anthropic
At the AI+ Science Summit in Washington, D.C., the Fireside Chat: Frontiers & Foundations brought together Jack Clark, co-founder and Head of Policy at Anthropic, and Ylli Bajraktari, CEO and President of the Special Competitive Studies Project (SCSP), for a wide-ranging discussion on the state and future of large language models (LLMs) and AI’s transformative potential. From…
-

Case Study – AI+ Materials Science: Exploring the AI Frontier in Material Innovation
At the AI+ Science Summit in Washington, D.C., the session titled “Case Study – AI+ Materials Science” brought together distinguished experts to discuss how artificial intelligence is reshaping materials science, from accelerating discovery to tackling long-standing industrial challenges. Moderated by Jake Yeston, Editor at Science magazine, this conversation featured James “Jim” Warren, Director of the Materials Genome Project at…
-

Ethereum is Ten: The Blockchain That Changed Everything
A Decade of Revolutionary Blockchain Innovation Transforms Global Finance On July 30, 2015, a young programmer named Vitalik Buterin launched an ambitious project that would reshape the entire digital landscape. Today, exactly ten years later, Ethereum stands as the world’s second-largest cryptocurrency and the foundational infrastructure for an entirely new digital economy. What began as a…
-
Hollywood Unchained: How Blockchain Is Rewriting the Script with Riaz Mehta
Are we all ready to discover how the future of entertainment is being rewritten—one blockchain at a time? Well, today we sit down with Riaz Mehta, the visionary CEO and founder of Ritestream, the production studio shaking up Hollywood’s old playbook! He’s creating a new breed of production studio that takes advantage of Web3 technology like…
-

What Is China Doing in Science?
A Dispatch from the AI+ Science Summit Last week, in the luminous halls of the Waldorf Astoria, Washington’s AI+ Science Summit convened a panel raising precisely the question that keeps policymakers, academics, and industry leaders awake: What is China actually doing in science, and what does it mean for the global order? Guiding us through…
-

The Privacy Revolution – What is Zero Knowledge and How Will it Change Everything with Jens Groth
Step into the cryptic, captivating world of privacy tech with Jens Groth, the Chief Scientist at Nexus and the very architect behind the Groth16 protocol, one of the most important breakthroughs in cryptography. In this episode, we decode the “magic words” of digital privacy, Zero Knowledge Proofs, ZKPs, ZK SNARKS—and reveal how they’re quietly transforming the internet,…
-

Building the Future of AI – Inside AXL’s Ambitious Mission with Dr. Daniel Wigdor
Step into the heart of Canada’s AI revolution with Dr. Daniel Wigdor—professor, inventor, and co-founder & CEO of AXL, one of the country’s most ambitious venture studios. In this episode, we uncover how AXL is transforming world-class research into high-growth companies and why its mission to launch 50 AI-powered ventures in five years could reshape Canada’s…
-

Meet Your Digital Twin: How Perspective-Aware Computing is Changing Collaboration
Cambridge, MA – MIT EmTechAI: Hossein Rahnama, Visiting Associate Professor at MIT Media Lab, Professor at Toronto Metropolitan University, and Founder/CEO of Flybits, presented a vision for the future of AI centered on Perspective-Aware Computing (PAC), also known as Perspective-Aware AI. His work explores how AI can move beyond personalization to foster deeper, more empathetic human-to-human and…
-

Guest Post: Experts release their most ambitious forecast: Bitcoin could reach $275,000 by 2025
By Jennifer Maldonado June 25th, 2025 Originally posted on Bit2Me Crypto News https://news.bit2me.com/en/expertos-lanzan-pronostico-ambicioso-bitcoin-a-275-mil-en-2025 Learn about the bold prediction that puts Bitcoin at $275,000 by the end of 2025 and what factors could drive this historic surge. Joseph Raczynski, analyst and futurist at JT Consulting & Media, has presented a bold projection that is generating a lot…
-

AI: The New Intern, Coach, and CEO-All in One?
Cambridge, MA – MIT EmTechAI: Jim Rowan, Head of AI at Deloitte, and Gabriele Ricci, Chief Data & Technology Officer at Takeda, shared a candid, practical look at how AI is reshaping organizations-from global consulting giants to leading pharmaceutical companies. Their discussion focused on building digital dexterity, managing change, and maximizing value while balancing innovation…
-

Unmasking Google’s Advertising Empire with Ari Paparo
Step into the world behind the web’s curtain, where a single company’s quest for dominance has shaped the digital age. In this episode, we sit down with Ari Paparo, founder of Marketecture.tv, former Google executive, and author of the forthcoming exposé, Yield: How Google Bought, Built, and Bullied Its Way to Advertising Dominance (Amplify, August 5, 2025). Why…
-

Lights, Camera, AI: Pinar Demirgad and the Next Act in Filmmaking
Cambridge, MA – MIT EmTechAI: Pinar Demirgad, Co-founder & CEO of Cuebric, delivered a compelling talk on how AI is transforming the landscape of visual storytelling. Drawing from her unique experience as both an artist and entrepreneur, she explored the current capabilities, limitations, and future directions of generative AI in film and content creation. From…
-

Vulcan Unleashed: How Amazon’s Next Wave of Intelligent Robotics Is Changing the Game
Cambridge, MA – MIT EmTechAI: When Scott Dresser, Vice President of Amazon Robotics, took the stage at EmTechAI, the room buzzed with anticipation. After all, this is the man who’s helped shepherd Amazon’s robotics revolution since the company’s acquisition of Kiva Systems in 2012 – a move that marked a watershed moment for both Amazon…
-

AI on the Blockchain: Building a Safer Digital Future with DecideAI
Jesse Glass, Lead AI Researcher at DecideAI, steps into the spotlight at a moment when the stakes for AI and data privacy have never been higher. As AI systems race ahead, so do the risks, exposing sensitive data in ways most current tech simply isn’t built to defend. Enter the “zero trust” philosophy: a world…
-

Beyond SaaS: How AI Agents Are Rewriting the App Playbook
Is the SaaS model on its last legs, or just evolving into something smarter? Today, most of us live in a world run by Software as a Service, but with the rise of AI, the rules of the game are changing fast. Enter Anton Marchanka, CEO of Zing Coach, a leader whose portfolio spans $100 million,…
-

Code Unleashed: How Poolside Is Making Waves in Generative AI
Cambridge, MA – MIT EmTechAI: Margarida Garcia, VP of Operations at Poolside, recently shared her perspective on the evolving landscape of generative coding and the unique innovations her company is bringing to the field. Poolside is building its own foundation model for code generation, with a focus on secure, enterprise-ready deployments. Here are the key…
-
Proof Without Peeking: Human Passport and the Future of Blockchain Identity
Imagine if verifying you’re human online didn’t mean giving up your privacy, or your entire transaction history. Today, blockchain’s biggest paradox is that while it promises trustless systems, it often leaves identities and wallets wide open, exposing users to everything from Sybil attacks to airdrop hunters. On platforms like Base, the Coinbase-backed Ethereum Layer 2…
-

Meet Your New Digital Sidekick: AI Agents Take the Wheel
Cambridge, MA – MIT EmTechAI: Yash Kumar and Reiichiro Nakano from OpenAI discussed the evolution and impact of AI agents-particularly OpenAI’s Operator-on digital interaction. Their conversation highlighted the technological progress, challenges, and future directions of AI agents as they move from simple chatbots to sophisticated digital assistants capable of performing complex, real-world tasks on behalf…
-

No-Code, No Lines: How Halliday Is Serving Up Instant Blockchain Innovation
What if building on the blockchain was as effortless as ordering your daily coffee, no cryptic instructions, no endless queues, just tap, pay, and play? Thanks to a wave of agentic AI and smart contract innovation, that future is now. Today, Fintechs and banks can launch digital asset products in hours, not months, all while…
-

Tailor-Made Intelligence: From Off-the-Rack to Runway-Ready AI
Cambridge, MA – MIT EmTechAI: Waseem AlShikh, CTO and co-founder of Writer, took the EmTech AI 2025 stage to share the remarkable story behind one of enterprise AI’s fastest-growing platforms. Writer’s journey began with a simple but powerful idea: AI should be practical, efficient, and tailored to the specific needs of each business. Founded in 2020,…
-
Control, Context, and Code: Windsurf’s Quiet Revolution in Developer Tools
Anshul Ramachandran, founding team member at Windsurf Ever wonder what happens when the future of software meets the sharpest minds in AI—right as acquisition rumors swirl? At the AI+ Expo in Washington, DC, I sat down with Anshul Ramachandran, founding team member at Windsurf (formerly Codeium), just as whispers of an OpenAI buyout electrified the halls. Ramachandran’s resume reads…
-

AI on the Edge: From Cat Videos to Cancer Cures
Cambridge, MA – MIT EmTechAI: Scott Penberthy, Senior Director of Applied AI in the Office of the CTO at Google Cloud, is no stranger to big ideas. In his talk, “New Frontiers in AI Models,” Penberthy offered a sweeping view of how the latest advances in artificial intelligence are reshaping industries, accelerating scientific discovery, and…